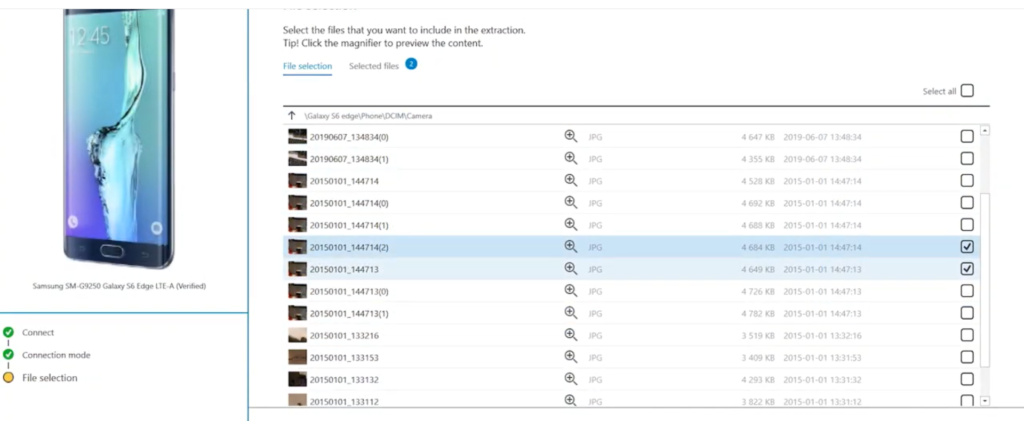
How to Find Location Data from Pictures
This short demo will show you how to find data location from Pictures gathered on any gadget using the extracted meta data with our Digital Forensic Solution
This short demo will show you how to find data location from Pictures gathered on any gadget using the extracted meta data with our Digital Forensic Solution

Desktop as a Service (DaaS) provisioned either Windows or Linux Desktops in just a few minutes and quickly scale up-to thoussand of desktops to workers across the globe. Access your business application anytime, anywhere on a high-speed low latency and higly secured network compared to traditional desktop and on-premises Virtual desktop infrastructure (VDI).
DaaS helps you to simplify your desktop delivery strategy and manageability, users get a fast responsive desktop of their choice that they can access anywhere; anytime from any supported devices.

Infrastructure Modernization Project by RECHNER DATEN TECHNIK INC.



📠Structured Cabling Data & Voice
🚨Firewall & Security
📂AD Server + O365
💿Software Licensing
👁️🗨️Managed Services & Support
Perform targeted extractions of Apple & Android devices with the Checkra1n exploit or by other means. Get critical data in ten minutes or less, with data from the most popular apps such as WhatsApp, WeChat, Facebook Messenger and others.
Logical is a rapid extraction method to access and recover live and file system data from the device right on the crime scene, by communicating directly with the operating system of the device.
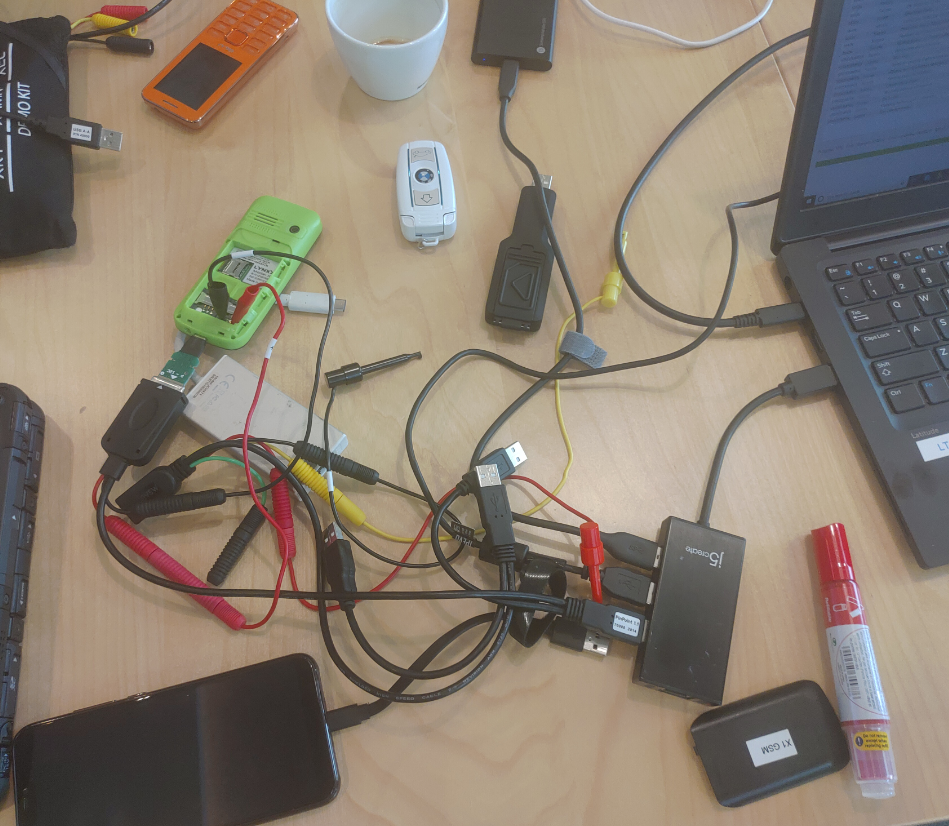
Physical lets examiners sidestep the operating system to dump all system and deleted data out of the device, plus it also allows you to overcome security and encryption challenges on locked devices.
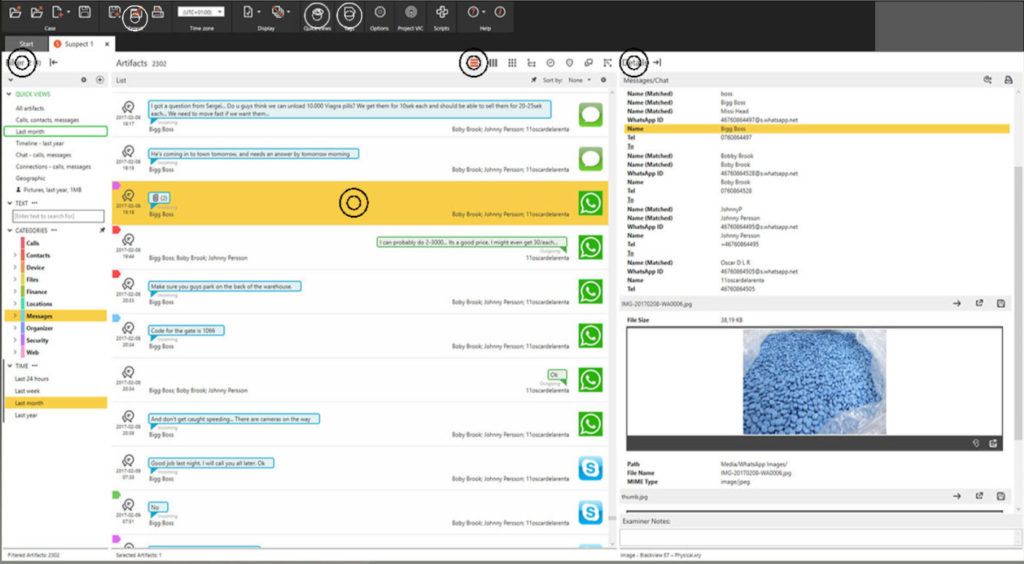
The amount of data stored on mobile phones and other mobile devices is dramatically greater today than ever before. That makes the challenges of searching, filtering and analyzing that data more daunting as well. You need to quickly find what you are looking for, even in huge data sets. Whether your mission is to gather and report intelligence, prevent crime or quickly produce solid evidence

Surveillance is the monitoring of behavior, activities, or information for the purpose of influencing, managing or directing. This can include observation from a distance by means of electronic equipment, such as closed-circuit television (CCTV), or interception of electronically transmitted information, such as Internet traffic. It can also include simple technical methods, such as human intelligence gathering and postal interception.
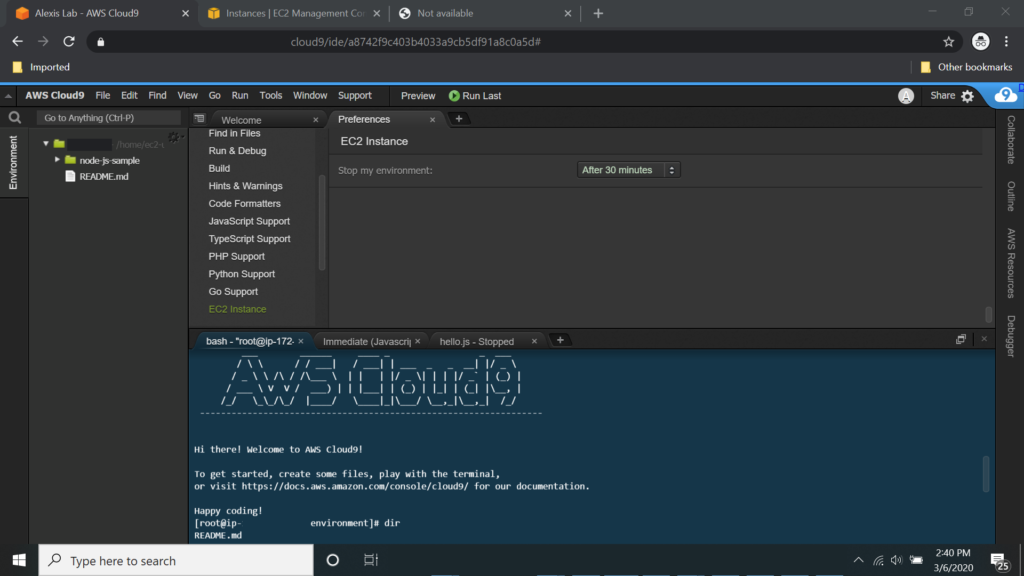
Platform as a service (PaaS) or application platform as a service (aPaaS) or platform-based service is a category of cloud computing services that provides a platform allowing customers to develop, run, and manage applications without the complexity of building and maintaining the infrastructure typically associated with developing and launching an app.

Infrastructure as a service (IaaS) are online services that provide high-level APIs used to dereference various low-level details of underlying network infrastructure like physical computing resources, location, data partitioning, scaling, security, backup etc. A hypervisor, such as Xen, Oracle VirtualBox, Oracle VM, KVM, VMware ESX/ESXi, or Hyper-V, LXD, runs the virtual machines as guests. Pools of hypervisors within the cloud operational system can support large numbers of virtual machines and the ability to scale services up and down according to customers’ varying requirements.

A web hosting service is a type of Internet hosting service that allows individuals and organizations to make their website accessible via the World Wide Web. Web hosts are companies that provide space on a server owned or leased for use by clients, as well as providing Internet connectivity, typically in a data center.

Cloud computing is the on-demand availability of computer system resources, especially data storage and computing power, without direct active management by the user. The term is generally used to describe data centers available to many users over the Internet. Large clouds, predominant today, often have functions distributed over multiple locations from central servers. If the connection to the user is relatively close, it may be designated an edge server.